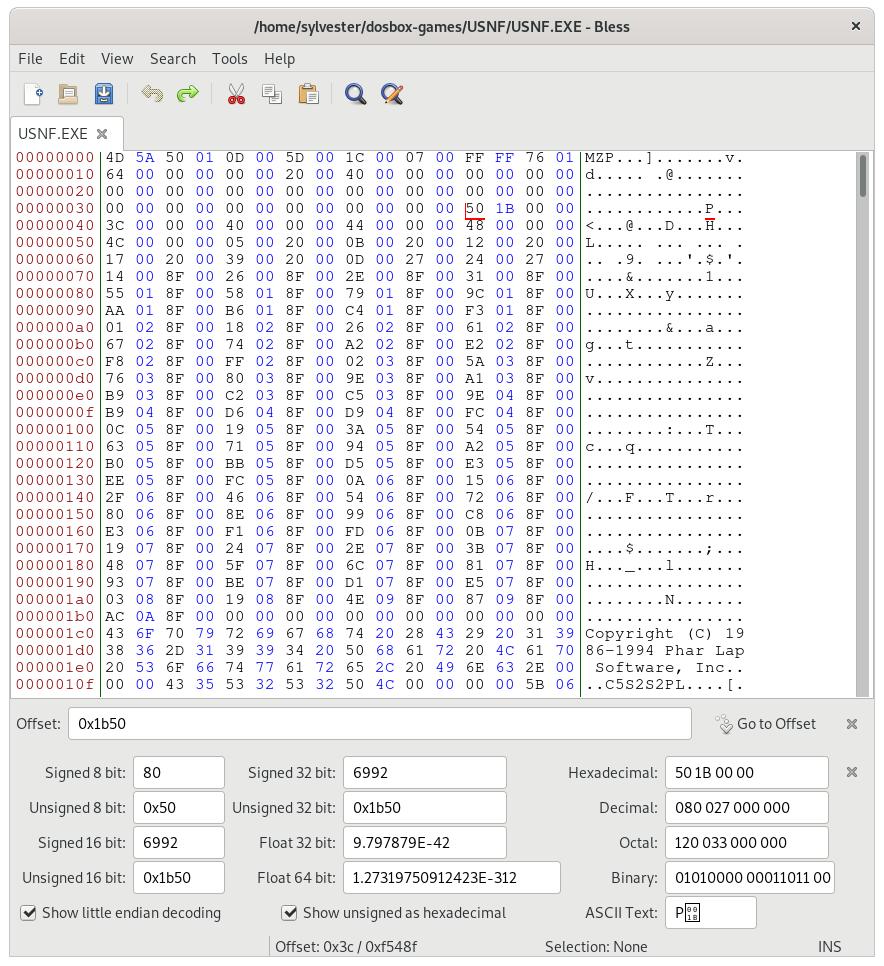
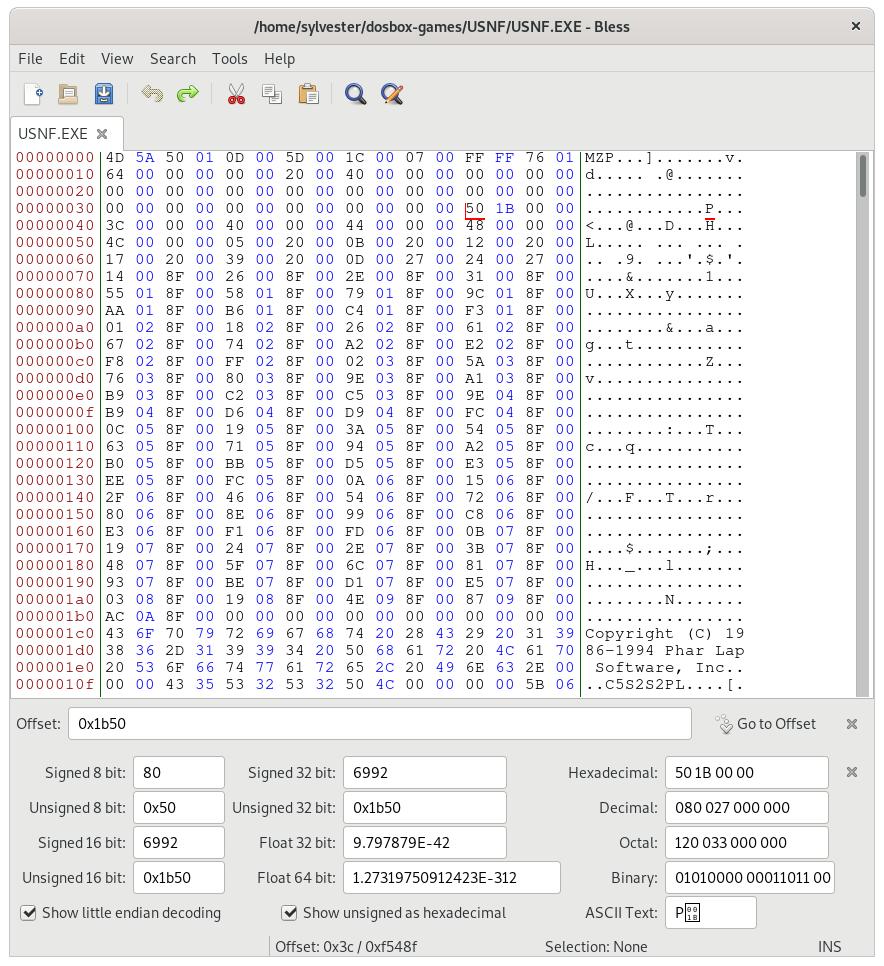
Continuing from where we left off, let's examine USNF.EXE in a hex editor, to get a better understanding of the file structure. The file command identifies the executable as MS-DOS executable. Loading into a hex editor:
Continue reading "A quick look into the DOS exe header and relocation table"
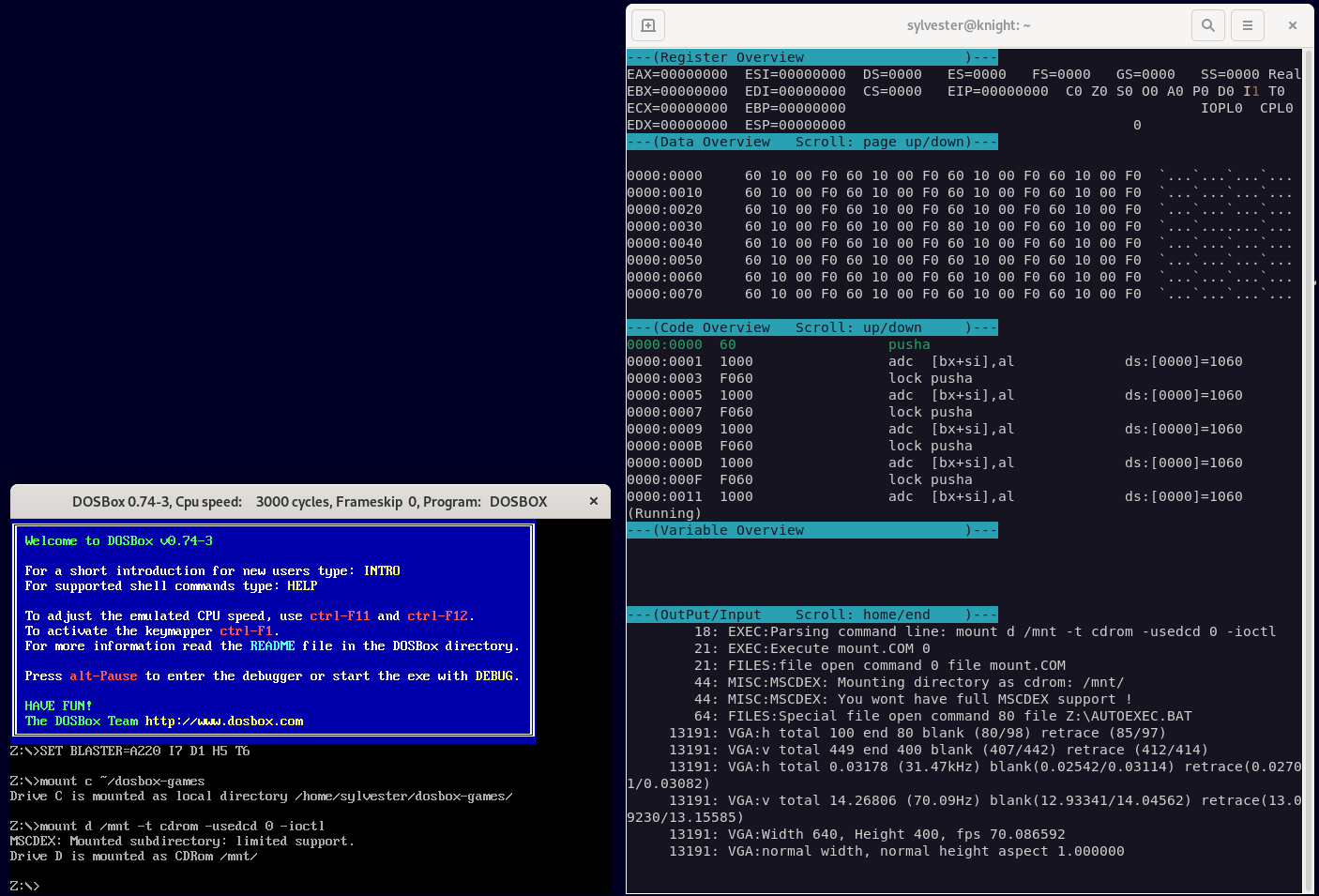
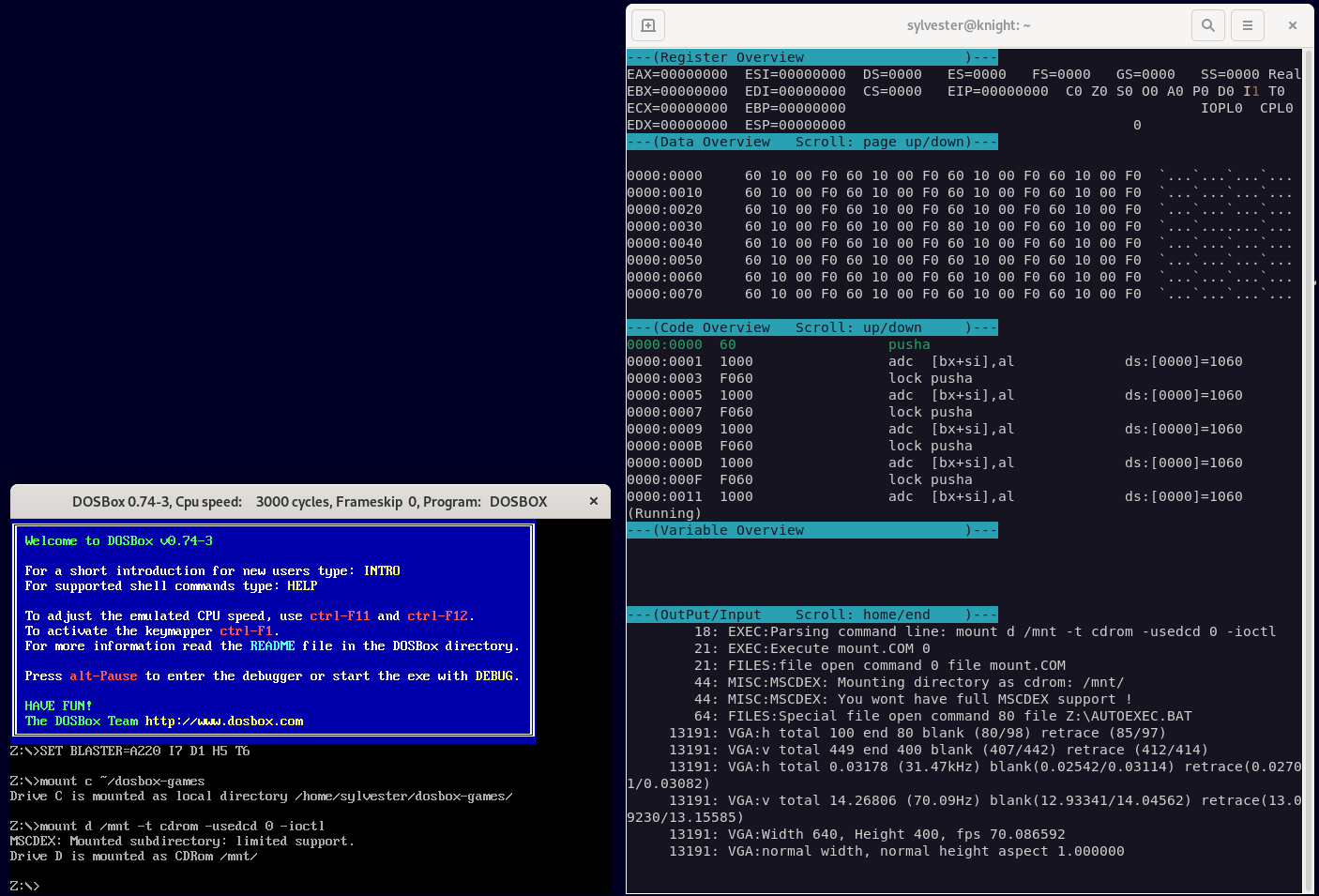
DosBox comes with it's own built-in debugger, which can be useful when reversing old DOS games.
This feature needs to be enabled at build time (--enable-debug or --enable-debug=heavy), so either download the special binary or build it from source. I went through the build process in a previous post: https://blog.aupcgroup.com/index.php?/archives/32-Hacking-a-DOS-32-bit-protected-mode-game-from-1997.html
This gives a nice view with registers, dissassembly and memory views:
This VOGONS thread has a quick summary on the DosBox built-in debugger: https://www.vogons.org/viewtopic.php?t=3944
Continue reading "Reverse Engineering with DOSBox debug build"
It's been a long time since I've looked at X86 assembly, and I thought it might be fun to reverse engineer a game I enjoyed playing when I was much younger - US Navy Fighters.
Hacking tools
IDA (Interactive Dissassembler) - download IDA 8.3 from https://hex-rays.com/ida-free/ (free for personal use). I'm using the linux version. To install chmod +xx the installer and accept the license agreement. Choose the install location, I chose idafree-8.3 in my home folder.
chmod +x idafree83_linux.run
./idafree-8.3/ida64
Debugger - USNF is a DOS game and won't run on linux natively, however it runs perfectly fine through DOS-Box. The good news is DOS-Box is available as a special debug build, with an integrated debugger. This allows us to set breakpoints, peek at memory locations, etc, and should very helpful in analysing the game. To get the debug build we'll need to build DOS-Box from source. Download the source code from https://www.dosbox.com. There is some information on the build process on VOGONS.
Download the file: dosbox-0.74-3.tar.gz, and run the build. Install autotools if it's missing. Also, note the SDL 1.2 and curses dependencies:
sudo apt install autoconf autotools-dev automake
sudo apt install libsdl1.2-dev libncurses-dev
tar xvf dosbox-0.74-3.tar.gz
cd dosbox-0.74-3/
./autogen.sh
./configure --enable-debug=heavy
make
sudo make install
By default, the binary is installed into /usr/local/bin. I renamed my binary to dosbox-debug to distinguish it from the standard version:
sudo mv /usr/local/bin/dosbox /usr/local/bin/dosbox-debug
Continue reading "Hacking a DOS 32 bit protected mode game from 1997"